Link to forum discussion:
[https://central.owncloud.org/t/owncloud-ldap-replica…-server-issues/6688]
### Steps to reproduce
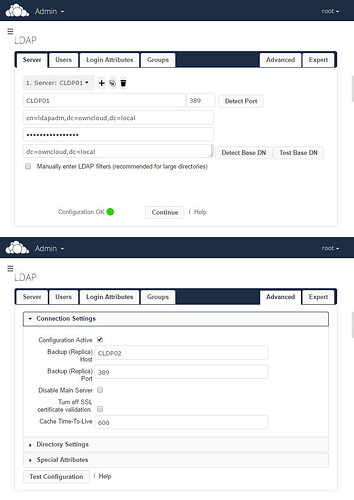
1. Configured single OpenLDAP server in Owncloud and tested (users can log in)
2. Configured replica OpenLDAP server and tested in OwnCloud (user can log in)
3. Configured OwnCloud LDAP so that the replica server settings in the Advanced tab are set to the second server
4. Turn off the primary LDAP server, try to log in (now using the replica (backup) server). Login fails- see actual behavious
### Expected behaviour
User should be able to log in using the backup LDAP server
### Actual behaviour
User cannot log in
### Server configuration
Operating system: CentOS 7-3.1611
Web server: httpd version 2.4.6
Database: MySQL
PHP version: CentOS 7-3.1611
ownCloud version: 9.1.4
Updated from an older ownCloud or fresh install: Fresh
Special configuration (external storage, external authentication, reverse proxy, server-side-encryption):
- Separate Database, Authentication and Storage servers, reverse proxy and server-side-encryption
**Where did you install ownCloud from:**
https://owncloud.org/install/
**Signing status (ownCloud 9.0 and above):**
```
Login as admin user into your ownCloud and access
http://example.com/index.php/settings/integrity/failed
paste the results here.
No errors have been found
```
**List of activated apps:**
```
If you have access to your command line run e.g.:
sudo -u www-data php occ app:list
from within your ownCloud installation folder
[root@COC01 ~]# sudo -u apache php /var/www/owncloud/occ app:list
Enabled:
- activity: 2.3.2
- comments: 0.3.0
- configreport: 0.1.1
- dav: 0.2.7
- encryption: 1.3.0
- federatedfilesharing: 0.3.0
- federation: 0.1.0
- files: 1.5.1
- files_pdfviewer: 0.8.1
- files_sharing: 0.10.0
- files_texteditor: 2.1
- files_trashbin: 0.9.0
- files_versions: 1.3.0
- files_videoplayer: 0.9.8
- firstrunwizard: 1.1
- gallery: 15.0.0
- notifications: 0.3.0
- provisioning_api: 0.5.0
- systemtags: 0.3.0
- templateeditor: 0.1
- twofactor_totp: 0.4.2
- updatenotification: 0.2.1
- user_ldap: 0.9.0
Disabled:
- external
- files_antivirus
- files_external
- user_external
```
**The content of config/config.php:**
```
If you have access to your command line run e.g.:
sudo -u www-data php occ config:list system
from within your ownCloud installation folder
or
Insert your config.php content here
(ATTENTION: WITHOUT the database password, passwordsalt and secret !!!)
{
"system": {
"instanceid": "oc47x9tjw1jc",
"passwordsalt": "***REMOVED SENSITIVE VALUE***",
"secret": "***REMOVED SENSITIVE VALUE***",
"trusted_domains": [
"redacted",
"redacted",
"redacted",
"redacted"
],
"datadirectory": "\/mnt\/glusterfs",
"htaccess.RewriteBase": "\/",
"dbtype": "mysql",
"version": "9.1.4.2",
"dbname": "owncloud",
"dbhost": "redacted",
"dbtableprefix": "oc_",
"dbuser": "***REMOVED SENSITIVE VALUE***",
"dbpassword": "***REMOVED SENSITIVE VALUE***",
"enable_previews": false,
"logtimezone": "UTC",
"log_type": "owncloud",
"logfile": "owncloud.log",
"loglevel": "2",
"installed": true,
"mail_smtpmode": "smtp",
"mail_from_address": "admin.owncloud",
"mail_domain": "redacted",
"ldapIgnoreNamingRules": false,
"appstore.experimental.enabled": true,
"mail_smtpsecure": "tls",
"mail_smtphost": "redacted",
"mail_smtpport": "25",
"trusted_proxies": [
"redacted",
"redacted",
"redacted"
]
},
"apps": {
"activity": {
"enabled": "yes",
"installed_version": "2.3.2",
"types": "filesystem"
},
"backgroundjob": {
"lastjob": "9"
},
"comments": {
"enabled": "yes",
"installed_version": "0.3.0",
"types": "logging"
},
"configreport": {
"enabled": "yes",
"installed_version": "0.1.1",
"types": "filesystem"
},
"core": {
"backgroundjobs_mode": "cron",
"default_encryption_module": "OC_DEFAULT_MODULE",
"encryption_enabled": "yes",
"installedat": "1489056684.1882",
"lastcron": "1489658939",
"lastupdateResult": "[]",
"lastupdatedat": "1491408812",
"oc.integritycheck.checker": "[]",
"public_files": "files_sharing\/public.php",
"public_webdav": "dav\/appinfo\/v1\/publicwebdav.php",
"shareapi_allow_resharing": "no",
"shareapi_default_expire_date": "yes",
"shareapi_enforce_expire_date": "yes",
"shareapi_enforce_links_password": "yes",
"umgmt_show_backend": "true",
"umgmt_show_email": "true",
"umgmt_show_last_login": "true",
"umgmt_show_storage_location": "true"
},
"dav": {
"enabled": "yes",
"installed_version": "0.2.7",
"types": "filesystem"
},
"encryption": {
"enabled": "yes",
"installed_version": "1.3.0",
"masterKeyId": "master_c76d7582",
"publicShareKeyId": "pubShare_c76d7582",
"recoveryAdminEnabled": "1",
"recoveryKeyId": "recoveryKey_c76d7582",
"types": "filesystem"
},
"federatedfilesharing": {
"enabled": "yes",
"installed_version": "0.3.0",
"types": ""
},
"federation": {
"enabled": "yes",
"installed_version": "0.1.0",
"types": "authentication"
},
"files": {
"cronjob_scan_files": "500",
"default_quota": "100 GB",
"enabled": "yes",
"installed_version": "1.5.1",
"types": "filesystem"
},
"files_pdfviewer": {
"enabled": "yes",
"installed_version": "0.8.1",
"ocsid": "166049",
"types": ""
},
"files_sharing": {
"enabled": "yes",
"installed_version": "0.10.0",
"types": "filesystem"
},
"files_texteditor": {
"enabled": "yes",
"installed_version": "2.1",
"ocsid": "166051",
"types": ""
},
"files_trashbin": {
"enabled": "yes",
"installed_version": "0.9.0",
"types": "filesystem"
},
"files_versions": {
"enabled": "yes",
"installed_version": "1.3.0",
"types": "filesystem"
},
"files_videoplayer": {
"enabled": "yes",
"installed_version": "0.9.8",
"types": ""
},
"firstrunwizard": {
"enabled": "yes",
"installed_version": "1.1",
"ocsid": "166055",
"types": ""
},
"gallery": {
"enabled": "yes",
"installed_version": "15.0.0",
"types": ""
},
"notifications": {
"enabled": "yes",
"installed_version": "0.3.0",
"types": "logging"
},
"provisioning_api": {
"enabled": "yes",
"installed_version": "0.5.0",
"types": "prevent_group_restriction"
},
"systemtags": {
"enabled": "yes",
"installed_version": "0.3.0",
"types": "logging"
},
"templateeditor": {
"enabled": "yes",
"installed_version": "0.1",
"types": ""
},
"twofactor_totp": {
"enabled": "yes",
"installed_version": "0.4.2",
"ocsid": "174726",
"types": ""
},
"updatenotification": {
"enabled": "yes",
"installed_version": "0.2.1",
"types": ""
},
"user_ldap": {
"cleanUpJobOffset": "0",
"enabled": "yes",
"has_memberof_filter_support": "",
"home_folder_naming_rule": "",
"installed_version": "0.9.0",
"last_jpegPhoto_lookup": "0",
"ldap_agent_password": "redacted",
"ldap_attributes_for_group_search": "",
"ldap_attributes_for_user_search": "",
"ldap_backup_host": "redacted",
"ldap_backup_port": "389",
"ldap_base": "dc=owncloud,dc=local",
"ldap_base_groups": "cn=owncloud,ou=Users,dc=owncloud,dc=local",
"ldap_base_users": "cn=owncloud,ou=Users,dc=owncloud,dc=local",
"ldap_cache_ttl": "600",
"ldap_configuration_active": "1",
"ldap_display_name": "cn",
"ldap_dn": "cn=ldapadm,dc=owncloud,dc=local",
"ldap_dynamic_group_member_url": "",
"ldap_email_attr": "mail",
"ldap_experienced_admin": "0",
"ldap_expert_username_attr": "uid",
"ldap_expert_uuid_group_attr": "",
"ldap_expert_uuid_user_attr": "",
"ldap_group_display_name": "cn",
"ldap_group_filter": "",
"ldap_group_filter_mode": "0",
"ldap_group_member_assoc_attribute": "uniqueMember",
"ldap_groupfilter_groups": "",
"ldap_groupfilter_objectclass": "",
"ldap_host": "redacted",
"ldap_login_filter": "(&(|(objectclass=posixAccount))(uid=%uid))",
"ldap_login_filter_mode": "1",
"ldap_loginfilter_attributes": "",
"ldap_loginfilter_email": "0",
"ldap_loginfilter_username": "1",
"ldap_nested_groups": "0",
"ldap_override_main_server": "0",
"ldap_paging_size": "500",
"ldap_port": "389",
"ldap_quota_attr": "",
"ldap_quota_def": "",
"ldap_tls": "0",
"ldap_turn_off_cert_check": "0",
"ldap_user_display_name_2": "",
"ldap_user_filter_mode": "0",
"ldap_userfilter_groups": "",
"ldap_userfilter_objectclass": "posixAccount",
"ldap_userlist_filter": "(|(objectclass=posixAccount))",
"types": "authentication",
"use_memberof_to_detect_membership": "1"
}
}
}
```
**Are you using external storage, if yes which one:** local/smb/sftp/...
glusterfs
**Are you using encryption:** yes/no
yes
**Are you using an external user-backend, if yes which one:** LDAP/ActiveDirectory/Webdav/...
OpenLDAP
#### LDAP configuration (delete this part if not used)
```
With access to your command line run e.g.:
sudo -u www-data php occ ldap:show-config
from within your ownCloud installation folder
Without access to your command line download the data/owncloud.db to your local
computer or access your SQL server remotely and run the select query:
SELECT * FROM `oc_appconfig` WHERE `appid` = 'user_ldap';
Eventually replace sensitive data as the name/IP-address of your LDAP server or groups.
+-------------------------------+--------------------------------------------+
| Configuration | |
+-------------------------------+--------------------------------------------+
| hasMemberOfFilterSupport | |
| hasPagedResultSupport | |
| homeFolderNamingRule | |
| lastJpegPhotoLookup | 0 |
| ldapAgentName | cn=ldapadm,dc=owncloud,dc=local |
| ldapAgentPassword | *** |
| ldapAttributesForGroupSearch | |
| ldapAttributesForUserSearch | |
| ldapBackupHost | redacted2 |
| ldapBackupPort | 389 |
| ldapBase | dc=owncloud,dc=local |
| ldapBaseGroups | cn=owncloud,ou=Users,dc=owncloud,dc=local |
| ldapBaseUsers | cn=owncloud,ou=Users,dc=owncloud,dc=local |
| ldapCacheTTL | 600 |
| ldapConfigurationActive | 1 |
| ldapDynamicGroupMemberURL | |
| ldapEmailAttribute | mail |
| ldapExperiencedAdmin | 0 |
| ldapExpertUUIDGroupAttr | |
| ldapExpertUUIDUserAttr | |
| ldapExpertUsernameAttr | uid |
| ldapGroupDisplayName | cn |
| ldapGroupFilter | |
| ldapGroupFilterGroups | |
| ldapGroupFilterMode | 0 |
| ldapGroupFilterObjectclass | |
| ldapGroupMemberAssocAttr | uniqueMember |
| ldapHost | CLDP01 |
| ldapIgnoreNamingRules | |
| ldapLoginFilter | (&(|(objectclass=posixAccount))(uid=%uid)) |
| ldapLoginFilterAttributes | |
| ldapLoginFilterEmail | 0 |
| ldapLoginFilterMode | 1 |
| ldapLoginFilterUsername | 1 |
| ldapNestedGroups | 0 |
| ldapOverrideMainServer | 0 |
| ldapPagingSize | 500 |
| ldapPort | 389 |
| ldapQuotaAttribute | |
| ldapQuotaDefault | |
| ldapTLS | 0 |
| ldapUserDisplayName | cn |
| ldapUserDisplayName2 | |
| ldapUserFilter | (|(objectclass=posixAccount)) |
| ldapUserFilterGroups | |
| ldapUserFilterMode | 0 |
| ldapUserFilterObjectclass | posixAccount |
| ldapUuidGroupAttribute | auto |
| ldapUuidUserAttribute | auto |
| turnOffCertCheck | 0 |
| useMemberOfToDetectMembership | 1 |
+-------------------------------+--------------------------------------------+
```
### Client configuration
**Browser:**
Chrome 56
**Operating system:**
Windows 10
#### ownCloud log (data/owncloud.log)
```
[root@nnnnnn ~]# cat /data/octest/owncloud.log | grep WNpAuktqk8x@yWV655AG3wAAAAU
{"reqId":"WNpAuktqk8x@yWV655AG3wAAAAU","remoteAddr":"10.1.10.n","app":"index","message":"Exception: {\"Exception\":\"OC\\\\ServerNotAvailableException\",\"Message\":\"Lost connection to LDAP server.\",\"Code\":0,\"Trace\":\"
#0 \\\/var\\\/www\\\/owncloud\\\/apps\\\/user_ldap\\\/lib\\\/LDAP.php(257): OCA\\\\User_LDAP\\\\LDAP->postFunctionCall()\\
n#1 \\\/var\\\/www\\\/owncloud\\\/apps\\\/user_ldap\\\/lib\\\/LDAP.php(43): OCA\\\\User_LDAP\\\\LDAP->invokeLDAPMethod('bind', Resource id #591, 'cn=andrew jones...', '***********')\\
n#2 \\\/var\\\/www\\\/owncloud\\\/apps\\\/user_ldap\\\/lib\\\/Connection.php(600): OCA\\\\User_LDAP\\\\LDAP->bind(Resource id #591, 'cn=andrew jones...', '***********')\\
n#3 \\\/var\\\/www\\\/owncloud\\\/apps\\\/user_ldap\\\/lib\\\/Access.php(1308): OCA\\\\User_LDAP\\\\Connection->bind()\\
n#4 \\\/var\\\/www\\\/owncloud\\\/apps\\\/user_ldap\\\/lib\\\/User_LDAP.php(137): OCA\\\\User_LDAP\\\\Access->areCredentialsValid('cn=andrew jones...', '***********')\\
n#5 [internal function]: OCA\\\\User_LDAP\\\\User_LDAP->checkPassword(*** sensitive parameters replaced ***)\\
n#6 \\\/var\\\/www\\\/owncloud\\\/apps\\\/user_ldap\\\/lib\\\/User_Proxy.php(67): call_user_func_array(Array, Array)\\
n#7 \\\/var\\\/www\\\/owncloud\\\/apps\\\/user_ldap\\\/lib\\\/Proxy.php(139): OCA\\\\User_LDAP\\\\User_Proxy->walkBackends('ajones', 'checkPassword', Array)\\
n#8 \\\/var\\\/www\\\/owncloud\\\/apps\\\/user_ldap\\\/lib\\\/User_Proxy.php(182): OCA\\\\User_LDAP\\\\Proxy->handleRequest('ajones', 'checkPassword', Array)\\
n#9 \\\/var\\\/www\\\/owncloud\\\/lib\\\/private\\\/User\\\/Manager.php(200): OCA\\\\User_LDAP\\\\User_Proxy->checkPassword(*** sensitive parameters replaced ***)\\
n#10 \\\/var\\\/www\\\/owncloud\\\/core\\\/Controller\\\/LoginController.php(177): OC\\\\User\\\\Manager->checkPassword(*** sensitive parameters replaced ***)\\
n#11 [internal function]: OC\\\\Core\\\\Controller\\\\LoginController->tryLogin(*** sensitive parameters replaced ***)\\
n#12 \\\/var\\\/www\\\/owncloud\\\/lib\\\/private\\\/AppFramework\\\/Http\\\/Dispatcher.php(159): call_user_func_array(Array, Array)\\
n#13 \\\/var\\\/www\\\/owncloud\\\/lib\\\/private\\\/AppFramework\\\/Http\\\/Dispatcher.php(89): OC\\\\AppFramework\\\\Http\\\\Dispatcher->executeController(Object(OC\\\\Core\\\\Controller\\\\LoginController), 'tryLogin')\\
n#14 \\\/var\\\/www\\\/owncloud\\\/lib\\\/private\\\/AppFramework\\\/App.php(99): OC\\\\AppFramework\\\\Http\\\\Dispatcher->dispatch(Object(OC\\\\Core\\\\Controller\\\\LoginController), 'tryLogin')\\
n#15 \\\/var\\\/www\\\/owncloud\\\/lib\\\/private\\\/AppFramework\\\/Routing\\\/RouteActionHandler.php(46): OC\\\\AppFramework\\\\App::main('LoginController', 'tryLogin', Object(OC\\\\AppFramework\\\\DependencyInjection\\\\DIContainer), Array)\\
n#16 [internal function]: OC\\\\AppFramework\\\\Routing\\\\RouteActionHandler->__invoke(Array)\\
n#17 \\\/var\\\/www\\\/owncloud\\\/lib\\\/private\\\/Route\\\/Router.php(280): call_user_func(Object(OC\\\\AppFramework\\\\Routing\\\\RouteActionHandler), Array)\\
n#18 \\\/var\\\/www\\\/owncloud\\\/lib\\\/base.php(891): OC\\\\Route\\\\Router->match('\\\/login')\\
n#19 \\\/var\\\/www\\\/owncloud\\\/index.php(54): OC::handleRequest()\\
n#20 {main}\",\"File\":\"\\\/var\\\/www\\\/owncloud\\\/apps\\\/user_ldap\\\/lib\\\/LDAP.php\",\"Line\":284}","level":3,"time":"2017-03-28T10:53:47+00:00","method":"POST","url":"\/index.php\/login","user":"--"}
```